Yuxin Chen (UChicago) - Machine-Augmented Humans as a Privacy Armor
Machine-Augmented Humans as a Privacy Armor
As a variety of connected sensing devices are being deployed everywhere, significant privacy issues arise since these devices can monitor and capture our (private) behaviors in forms of image, video and sound. Leaked private data can be used by adversaries to launch significant privacy attacks against us.
In this thesis proposal, we explore the idea of protecting personal privacy by augmenting humans with low-cost machines.
First, we propose a new biometric authentication system that does not rely on privacy-sensitive face or voice information and is highly robust against data breach or leakage. Our system, ElectricAuth, authenticates a user by stimulating the user’s forearm muscles with a sequence of electrical impulses (i.e., a challenge) and measuring the user’s involuntary finger movements (i.e., response to the challenge). It uses muscle stimulation to produce as many as 64 million “one-time passwords” per user, using just 1 second of stimulation. Attackers replaying previously used responses (which is equivalent to using expired one-time passwords) will be rejected. This effectively resists the significant threat of data breach/leakage that faces today’s user authentication systems.
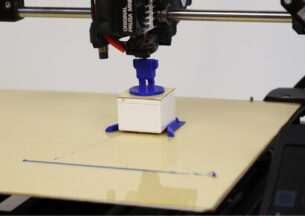
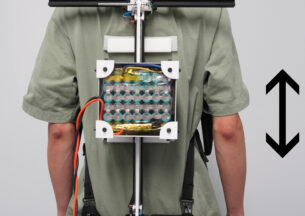
Second, we engineer a wearable microphone jammer (in the form of a bracelet) that prevents attackers from recording our speech content. Our bracelet jammer emits inaudible ultrasonic noise that disables microphones in the wearer’s surroundings, including hidden microphones. This design leverages a microphone hardware property that when exposed to ultrasonic noise, commodity microphones will leak the noise into the audible range, which disrupts the speech recordings. Furthermore, our wearable jammer increases the jamming coverage by exploiting the naturally occurring movements that users induce on their wearables as they gesture or walk.
Finally, we are exploring the design of a voice identity obfuscator to resist unauthorized user identification and voice cloning. Different from our microphone jammer, we will design new forms of obfuscating signals to effectively disrupt voice features related to user identity but not speech content.
Host: Advisors: Ben Zhao and Heather Zheng